Cloud Infrastructure Entitlement Management (CIEM) is a cloud security framework focused on managing and securing identities and permissions within an organization’s cloud infrastructure. Companies adopt CIEM to manage complex entitlements and mitigate cloud access risk across cloud providers such as Amazon Web Services (AWS), Google Cloud Platform (GCP), and Azure.
Teams use CIEM solutions to identify and mitigate risks associated with excessive permissions, unused identities, and misconfigured access controls. These tools also help companies meet regulatory compliance standards, enforce principle of least privilege, and enhance their overall security posture by providing deeper visibility and control.
CIEM Use Cases
There are four primary use cases for CIEM:
- Visibility of entitlements: Understanding and managing resources and access across cloud environments
- Discovering anomalies: Identification of unusual or risky patterns within entitlements that may raise security issues
- Automating compliance: Automation of processes—such asuser access reviews—to ensure compliance with various policies and regulations associated with cloud environments to minimize access risk.
- Removal of unused entitlements: Identification and removal of cloud permissions that are no longer necessary
CIEM Solution Capabilities
Some of the key capabilities of CIEM solutions include:
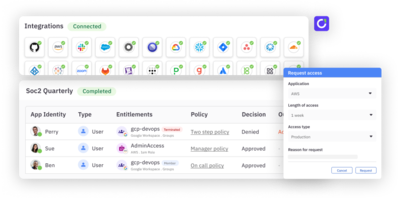
- Multi-cloud visibility: CIEM solutions provide deep visibility and control of permissions across a company’s cloud infrastructure, leveraginginteractive graphs to map access paths between roles and end users, including roles that are inherited and not directly assigned.
- Centralized dashboard: CIEM tools also provide a centralized dashboard from which users can monitor and control permissions across multiple cloud services such as amazon web services and azure.
- Access management: Bymanaging entitlements to applications, CIEM tools ensure that only authorized individuals are able to use open cloud resources and sensitive data.
- Risk assessment and prioritization: CIEM solutions identify and assess risks like excessive or unused entitlements and can prioritize remediation based on the level of risk certain entitlements or applications pose.
- Automated remediation: Once issues have been identified, security teams can automatically remediate risks by revoking cloud permissions or removing certain access rights in accordance with compliance requirements.
- Anomaly detection: CIEM tools can also calculate baseline activity to identify events that may be indicative of security threats, such as unusual insider activity, compromised credentials, unauthorized access or stolen access keys, to help organizations proactively mitigate attacks.
- Access activity and change monitoring: Cloud security solutions are also used to track which applications users are accessing and when. This functionality is key for identifying security incidents as well as keeping an audit trail for various compliance requirements.
CIEM solutions help companies centralize, manage, and protect access to cloud infrastructure environments. To learn more about how ConductorOne can help secure your cloud infrastructure, check out ourcloud security solutions ortalk to our team.