Privilege misuse and credential theft continue to be the leading causes of data breaches. According to IBM’s Cost of a Data Breach Report 2024, compromised credentials and phishing topped the list of attack vectors in the last year, and ConductorOne’s 2024 Identity Security Outlook Report found that 77% of surveyed organizations experienced a cyberattack or data breach in the past 12 months due to improper access or overprivileged users.
The more identities with privileged access to your network and sensitive data, the greater the risk of privilege misuse and privileged credential theft. The solution is to apply the principle of least privilege (PoLP) to your organization’s access control strategy.
Defining least privilege
Least privilege is a cybersecurity principle that states that a user or program should have the least amount of access necessary to perform their intended function. In other words, a user or program should only have access to the resources and permissions that are required to complete the task at hand, and no more. This principle is used to minimize the potential damage that can be caused by a security breach or by a user or program with malicious intent.
Least privilege limits the number of identities with access to networks, apps, data, programs, and processes to only those who require access. Privilege is attached to human users and non-human identities, such as API keys, industrial control systems, Internet of Things (IoT) devices, and more, and it is most often assigned based on the user’s job duties or the non-human identity’s role within an application.
However, far too often privileges aren’t revoked after they are no longer needed (e.g., a user changes jobs or the function of the non-human identity is completed) or access privileges are assigned to too many users. This opens up opportunities for malicious hackers to gain access to critical systems or data through human error, vulnerabilities, or misuse.
Authentication, authorization and accounting
Authentication, Authorization and Accounting (AAA) security is an access control framework. Authentication identifies each user or identity, authorization determines their access permissions, and accounting measures the resources accessed by the user. Overall, AAA security is an important component for managing access, but when looking at the principle of least privilege, authorization is the most vital factor. To achieve least privileged access, organizations must authenticate the user and their specific needs for access to accounts and applications within the network infrastructure, and then determine how much access is needed, either full control or limited activity. An organization could legitimately have hundreds of users who can be authenticated for full network access, but that doesn’t mean they should be authorized to access everything. That’s where the principle of least privilege comes in. Authenticated users are limited to authorization based on their job functions.
How to determine least privilege
No two authenticated identities will have the same privilege needs. Some employees in the IT or security department may require a “superuser” status (i.e., someone who needs access to all or most accounts, applications, and processes across the organization). But how do you determine the level of privilege a user should have?
Start with a privilege audit of the system infrastructure. You cannot assign privilege without intimate knowledge of every account, application, program, or process within the organization and the exact permissions needed for each one to operate. Audits should be done regularly to ensure privileged access is kept at a minimum level.
Once the audit of the system is completed, a similar audit of human user access is also necessary. Every user within the organization’s network should have a well-defined list of what type of access is required to conduct their job duties efficiently and effectively. Any new users should be assigned minimal privileges and access permissions can be increased (or decreased) as their specific tasks require.
How organizations can implement least privilege
Some strategies organizations can implement to enforce least privilege are:
- Define roles and permissions: Clearly outline user roles and assign specific permissions based on job functions. This can be done through a role-based access control (RBAC) model. RBAC helps avoid the provisioning of broad access rights and ensures that users only have the necessary privileges to perform their tasks, minimizing the potential for unauthorized actions.
- Automatically rotate credentials for privileged accounts: Regularly changing passwords for high-privilege accounts reduces the risk of unauthorized access and minimizes the potential damage in the case of an incident. By using automated password rotation, you can lock out users who no longer need access to privileged accounts and prevent individuals with malicious intent from cracking passwords.
- Segment networks: Isolating sensitive systems and data from the rest of the network limits the potential impact of a security breach. This segmentation should be carried out on the basis of the type of sensitive data stored and which users need access to it. This prevents lateral movement by attackers who have made their way into your environment, as their access is limited to the network they managed to breach.
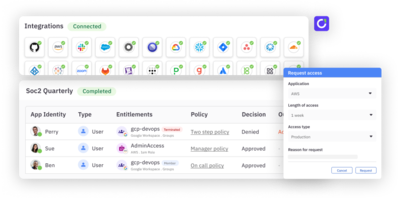
- Invest in a privileged access management (PAM) solution: Privileged access management (PAM) solutions centrally manage and control privileged accounts, reducing the risk of unauthorized access. These accounts can range from local administrator accounts to non-human service accounts, and you can even extend PAM principles to standard accounts. By limiting the number of individuals with elevated privileges, PAM helps enforce the principle of least privilege.
- Regularly audit privileges: Periodically reviewing user access rights helps companies hone in on the privileges users need to carry out their job functions and limit access to unnecessary privileges. This ongoing process ensures that users only have the access they need, minimizing the company’s overall attack surface.
- Enforce multi-factor authentication (MFA): Requiring multi-factor authentication (MFA) for all user accounts adds an extra layer of security, making it more difficult for end users to gain unauthorized access to critical systems, cloud environments, and other operating systems. In the scenario that credentials are compromised, MFA can prevent bad actors from gaining access to your systems.
Non-human identities and least privilege
Non-human identities refer to digital entities that are not human, such as software programs, robots, and autonomous systems. These entities can be assigned unique identities and are often given the ability to interact with the physical world and with other systems or entities. They typically have access to specific resources and permissions and are granted access to these resources based on their identity and the principle of least privilege.
With the push for digital transformation, organizations want DevOps teams to create new applications and get them to market as quickly as possible. This has led to the rise of non-human identities that play a role in the DevOps process. Like human users, non-human identities fall victim to privilege creep, leaving open vulnerabilities. These identities should be held to the same privilege standards and access controls as human users, the primary difference being that least privilege access for non-human identities must be monitored by a human to guard against unusual behaviors that could present security risks.
Benefits of least privilege
There are several benefits to enforcing the principle of least privilege:
- Decreases the threat of data breaches, insider threats, and credential theft
- Helps the organization to show compliance to federal and industry regulation requirements
- Reduces the attack surface, decreasing the risk of cyber attacks or malware spread
- Allows the organization to track user behavior
- Decreases the risks of human error
- Supports overall better security posture
To learn more about least privilege and how it compares to a zero trust security model, check out our least privilege vs. zero trust glossary post. To get practical steps for implementing least privilege, head over to our guide, 7 Principles for Least Privilege Access Implementation.