Every employee in your company has user access permissions to some area of your network infrastructure. It could be nothing more complicated than access to email and time-tracking software, but most workers need access to much more than that.
Few employees stay in the same job or have the job functions over the life of their career. When they change jobs, chances are their access permissions should change—some added, some deleted. But is that actually happening?
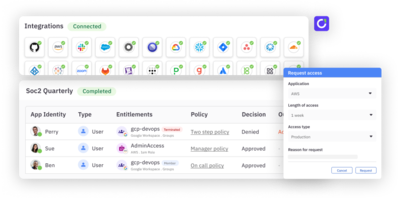
To keep track of user access permissions, organizations need to conduct periodic user access reviews. These reviews are not just a smart security move to protect the company assets; they are often required by federal and industry regulatory compliance rules.
What is a User Access Review?
A user access review is a periodic audit of access rights to verify that users and accounts have proper authorization to access networks and applications. Periodic user access reviews take a close look at users’ permissions levels, what they are allowed to access, and if they have legitimate and valid reasons for that access.
The review process is also an opportunity to verify users’ employment status within the organization, and how that impacts their access permissions. It’s not uncommon to discover employees who have moved to new departments and have taken on different job responsibilities that change access requirements. The review is also a good time to identify “orphaned” accounts – i.e., active accounts for users who have left the organization or whose privilege has expired, and whose credentials should have been deactivated.
User access reviews are typically conducted by the user’s manager or someone higher up in the management chain. The reviewer evaluates the user’s role, the access and privileges required by that role, and the level of credentials the user has.
What is the purpose of user access reviews?
The point of the periodic user access review is to discover potential risk to the organization caused by incorrect or outdated user privileges. The review is designed to uncover issues like privilege creep, mistakes or changes in user roles, access abuse or outdated policies.
How often should user access reviews be conducted?
Compliance regulations dictate how often organizations are required to perform access reviews. These regulations also have specific requirements for user access management. A few of the requirements are as follows:
- PCI DSS: The Payment Card Industry Data Security Standard PCI DSS Requirement 12 states “that an access control policy should be reviewed at least once a year.” In addition, PCI DSS Requirement 7 defines mandatory access measures that must be followed to meet compliance.
- HIPAA: Anyone required to follow the Health Insurance Portability and Accountability Act of 1996 (HIPAA) will need to follow code §164.308, which outlines administrative safeguards around policies for periodic user access reviews and implements standards around user access to meet compliance. These policies and procedures are reviewed during compliance audits.
- NIST: Although NIST is a non-regulatory agency, its cybersecurity frameworks are internationally followed standards. The NIST Risk Management framework, SP 800-53, directs organizations to perform periodic user access reviews and examine and update policies around access. Organizations can set the schedule for conducting the reviews. However, not performing periodic user reviews can lead to penalties and fines during compliance audits.
- Sarbanes-Oxley (SOX): Sarbanes-Oxley Act of 2002 sets auditing and financial regulations for public companies. In Section 404 of SOX it requires a “report on the assessment on the effectiveness of the internal control structure and procedures for financial reporting,” and sets enforcement of digital records with periodic user access reviews. There is annual compliance audit for SOX.
Best practices for reviewing user access:
Unless required by compliance standards, periodic user access reviews are up to the organization. There are some basic best practices to follow to ensure an efficient and effective process:
- Set up a user access review policy. The policy should outline: applications and data that qualifies as “sensitive” and require strict access policies, the breakdown of corporate access privileges (who has them and why), what the overall risk aversion level is, and what tools are already in use to mitigate risk and monitor user access.
- Establish a written user access review procedure. This procedure will include: the cadence for access reviews, determining review managers/officers, and deadlines for releasing the result of the review campaign.
- Implement the principle of least privilege via temporary access grants. For users who will only need access for a one-time job duty or for third-parties who need access for a contracted job, just-in-time temporary access will help to decrease the risk of orphaned accounts.
- Awareness training for the entire staff. Users should understand their role in access permissions and they should be involved in reviews about access rights. The more comfortable employees are about the risks involved with unnecessary access privileges, the easier the communication across departments and with IT/security teams will be.