Birthright access refers to the automatic granting of access privileges and permissions to certain resources based solely on an individual’s affiliation or position within an organization. This means that individuals are granted application and systems simply because of their job, rather than based on a specific need or request for access.
What are examples of birthright access?
One example of birthright access is a new employee in the finance department. They may be automatically granted access to critical financial systems such as Netsuite and other SaaS applications, regardless of whether they actually need access to all of them on day one.
Another example of birthright access is a new user on the engineering team. They may be granted specific roles and permissions in their Amazon Web Services (AWS) and GitHub environments that allow them to build, test, and deploy code.
What are the benefits of birthright access?
While birthright access can pose certain risks to an organization’s identity security posture, there are some potential benefits such as:
- Streamlined access management: By granting birthright access privileges, organizations can simplify the process of granting access. This can help reduce the workload of IT staff and streamline the access management processes.
- Improved productivity: Birthright access can help employees access the systems and data they need to perform their job duties more quickly and efficiently. This can lead to improved productivity and job satisfaction.
- Enhanced collaboration: Birthright access can promote collaboration between employees by enabling them to access the same systems and data needed to complete a project or task. This can help improve teamwork and productivity.
How is birthright access managed?
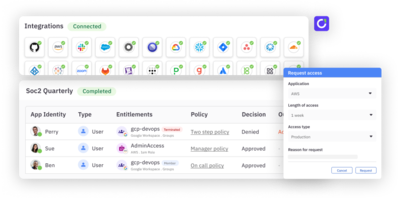
Birthright access is typically granted via an identity and access management (IAM) system and/or an identity governance and administration (IGA) platform. These systems automate the provisioning and de-provisioning of user access based on predefined roles and policies. When an employee joins an organization, these systems automatically assign access rights and permissions aligned with their job role, department, and responsibilities, ensuring they have the necessary tools and data to perform their duties effectively from day one. This on-boarding process leverages role-based access control (RBAC) or attribute based access control (ABAC), where roles are defined with specific access permissions, and users are assigned to these roles accordingly. IAM and IGA systems continuously monitor and update access rights as employees change roles, get promoted, or leave the organization, maintaining compliance with security policies and reducing the risk of unauthorized access. By centralizing and automating these processes, organizations can ensure efficient, secure, and compliant access management throughout the employee lifecycle.
Why is birthright access a potential security risk?
Birthright access can be dangerous if misused because it grants individuals access to resources or systems based solely on their job or position within an organization, rather than based on a specific need for access. This approach can lead to security risks, including an increased risk of data breaches and vulnerabilities.
Organizations that overly rely on birthright access for granting access may expose themselves to significant security risks, since this approach is counterintuitive to the principle of least privilege. Many times birthright access can be abused, in the sense that users are over permissioned to save on time of on-boarding, even though the majority of users do not need the access on a regular basis.
How to mitigate birthright access risks?
Granting too much birthright access can pose significant security risks as it may over privilege new hires immediately to sensitive data. Accordingly, there are several mitigating approaches to birthright access, all of which follow the best practice of least privilege access control:
- Self-service enablement: pushing more apps and permissions to self service access requests allows end users to request access to apps, permissions, and user roles when they need it.
- Just-in-time access (JIT): moving sensitive access to JIT, where access is granted based on access policies that force correct approvals and subsequent access is time bound, ensuring that access is not retained longer than needed.
- Access review automation: ensuring that all access is certified using periodic access reviews can help remove unused entitlements, even if they are granted as a part of the on-boarding or birthright access workflow.
- Refine roles definitions: take a hard look at the access users need as a part of their job functions and prune the permissions granted to these roles if only used irregularly.
- Automate removing unused access: using an access management or identity governance system, you can automate the deprovisioning of access that is not used.
All of these mitigations follow the principle of least privilege, which means that individuals are granted access only to the resources they need to perform their job responsibilities. This approach helps to limit the potential impact of a security breach or data leak by reducing the number of individuals who have access to sensitive data or systems.
Summary
Birthright access is when individuals are given access to specific data or systems because of their job or position at a company, rather than if they actually need access to the resources. Granting default access like this undermines the principle of least privilege and opens the door to numerous security threats and other malicious activities. Implementing access controls can help to reduce the negative effects of birthright access and can increase a company’s overall security posture.