ConductorOne’s company mission is to “secure the workforce.” That mission guides how we’re designing our platform to help companies secure identity, a major risk vector in modern cloud-first and hybrid environments. It also guides our internal approach to protecting our customers’ and our own data. Securing the workforce means considering all the ways information can be put at risk by the way we work and establishing a multilayered workforce security framework.
Balancing protection and productivity
We take a zero trust approach to workplace data security, meaning we treat all users, devices, and systems interacting with our network as potentially compromised. A zero trust perspective assumes breaches will happen, and so looks at defense in depth—how can we both stop the majority of breaches in the first place and reduce the impacts of those that will inevitably occur? Broad-based phishing attacks in particular have become so sophisticated and common—and will only get better and cheaper with the use of AI—that we have to assume it’s just a matter of time before one will be successful.
Our mandate is not only to train our team well and protect our devices but also to limit permissions and privileges so a compromised user or device can’t get far. As seen with the recent Reddit phishing incident, putting multiple complementary security tactics in place creates choke points that detect and thwart attacks before they can have much negative impact.
Of course the challenge vexing any business trying to stay a step ahead of hackers has always been balancing the tension between security and productivity. Lock down your networks and devices too well and you’ll just block and frustrate your staff. But make no productivity trade-offs for security and you’ll leave your data too vulnerable.
Our solution is a three-tiered system that buckets our data into ascending levels of sensitivity. We protect all three tiers at the base with strong identity authentication measures and then build more restrictive authentication and authorization fences around each higher tier. Productivity trade-offs are highest at the top tier, but those trade-offs are aligned with the level of protection that data tier demands. Here’s what our system looks like in practice.
Tier One
The information in this bucket, while private, wouldn’t cause much pain for our customers, our employees, or our business if exposed. Though it might be mildly embarrassing to have the broader public know, say, our favorite playlists or in-office snack preferences, a leak of this type of information doesn’t constitute serious harm to our business. That said, we want to protect all our information and retain the trust of our customers and industry, so we surround even this first category of internal data with strong protections.
Authenticating users AND their devices
We consider Single Sign-on (SSO) and multifactor authentication (MFA) minimum-level security protocols. And while many companies use push-based authentication and SMS-delivered OTPs for MFA, mainly because they’re easy, we don’t find these methods protective enough. Identity authentication is always coupled with a device—employees are using computers, tablets, and smart phones to interact with our systems—so non-credential-based authentication tools like passkeys and FIDO2 tokens that authenticate both users and their physical devices are currently the best way to do MFA.
On-device passkeys like Apple Touch ID can be easier to deploy across a workforce, but they’re not portable, which complicates users’ ability to switch workstations and use mobile devices. Physical keys present a greater upfront adoption challenge, especially for larger organizations, but for us, the initial distribution and training effort is worth effectively reducing phishing vulnerability to zero, so our entire staff uses YubiKeys. Larger companies may choose to provision a subset of employees—a specific department or users with access to particularly sensitive information—and roll out more gradually from there.
Learn more: How to Roll Out Passkeys and Block Phishing Attacks
Tier Two
This level can be roughly classified as information that’s business sensitive but not business critical, meaning its exposure would be detrimental but not fatal to our business. This level is the hardest to neatly categorize, and every company will have their own interpretation, based on their workflows, customers, and industry, of what belongs in this middle bucket.
We put most company communications and the data involved in and produced by our everyday work into this category. The majority of that data lives in SaaS apps of one variety or another—communication tools like Slack and Gmail, productivity tools like G Suite, design tools like Figma—so our goal is to securely manage access to these tools without too strictly limiting our employees’ ability to do their jobs.
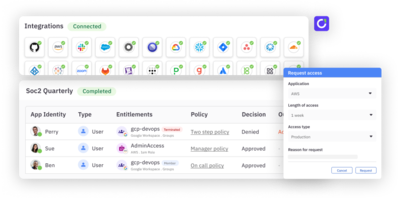
Enforcing least privilege access
This is where a modern approach to identity security is crucial. Following the principle of least privilege, we grant employees access only to those apps they need to perform their role, and we grant privileged access only for as long as it’s needed. Our ultimate goal is to achieve zero standing privilege (ZSP), where no employee or entity has privileged access on a standing basis, greatly reducing the chances of privileged access being exploited by an attacker.
The challenge of ZSP is limiting privileged access without hampering employees’ ability to get their work done. Putting modern access controls in place like just-in-time (JIT) access and easy, automatic provisioning and deprovisioning allows ZSP to be achieved without creating much of a productivity hit.
Go deeper: A Practical Approach to Achieving ZSP
Tier Three
The top tier comprises our customers’ data, which for the most part lives in our production environment. Protecting this data is paramount, and attacks on this type of data can be incredibly targeted and sophisticated, so this bucket has the most fences built around it. No one fence can keep all attackers out on its own, but each adds an additional layer of security—if one or more fail, the others are there to stop or at least greatly limit attacker access. Each fence also adds a layer of complexity to how we work, but we accept that complexity as a necessary condition of keeping our customers’ data secure.
Implementing multiparty authorization for the most sensitive data
In addition to using YubiKeys and restricting privileged access, we require developers interacting with data at this level to use isolated Chromebooks that access our production environment via Twingate, which is a software-defined VPN that provides direct authenticated access to private infrastructure. Sure, juggling multiple laptops and taking extra steps to get authenticated and authorized to perform certain functions are inconveniences, but they’re well worth the additional security layers provided.
Learn more: Architecting Zero Trust: Twingate + ConductorOne
Evolving to meet new threats
Some organizations, especially those working in fields with strict compliance protocols like FedRAMP or HIPAA, may include a fourth level of data that requires highly specific security measures. But for our purposes, these three tiers currently capture the levels of security needed to keep all the data we work with safe.
As technology and the ways it can be exploited inevitably evolve, we’ll continue to adapt our workforce security stance. Following zero trust to its logical conclusion, our endgame will likely be to implement full multiparty authorization across the board—it’s simply best practice to not trust any one party in a system. But that’s a journey we’re still on, and we’ll continue to revisit and share our experiences with our community as we grow.