In the fast-paced environment of the modern, cloud-forward company, strategies for securing infrastructure and identity are changing at a breakneck pace. We believed (and were told) MFA was sufficient for securing access in the cloud. This simply is not true. There are many ways to compromise identities, and over privileged users now represent one of the biggest threats to companies. Traditionally, this problem would fall under the purview of a Privileged Access Management (PAM) solution. But, companies are finding these legacy solutions frustratingly insufficient, thanks to the growing complexity of cloud environments, the need to achieve least privilege access, and the disconnect between older technical approaches and how modern identity and access is managed.
The downfall of traditional PAM
Traditional PAM solutions are becoming increasingly obsolete in the cloud forward world. By 2025, Gartner predicts that 51% of IT spending will shift from traditional solutions to the public cloud, compared to 41% in 2022 –– so the trend is already well underway. This shift in adoption is underpinned by fundamental technical shifts. Legacy PAM solutions focused on the “credential,” that is, the password or token that was used to log in to an account, machine, or service. These credentials were “checked in” and “checked out” from a PAM solution. Then, once the user was finished using the credential, it was rotated (hopefully, fingers crossed!). But this just isn’t how the cloud works.
It’s authorization, stupid
In the cloud, it doesn’t make sense to use shared accounts or checked out credentials. By and large, companies use a central identity provider that then authenticates the user into the downstream service. You don’t “check in” or “check out” the password for your primary account - you simply log in. The difference is authorization. What are you allowed to do once you log into a downstream service, cloud infrastructure provider, or application? That is authorization. And the challenge today is that users are very over-permissioned; employees, contractors, and service accounts have way too much access, and most of it is not used on an ongoing basis. That means that digital identities have become the biggest threat to compromising your organization.
The rise of least privilege access and just-in-time permissions
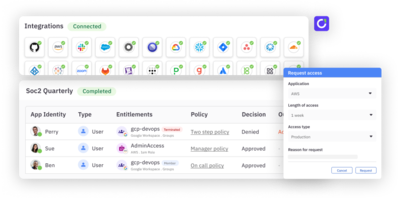
Securing identity in the cloud means executing on least privilege access. Least privilege access means getting users the access they need to perform a job, for as long as they need to perform the job, and for no longer. This requires companies to move away from “birthright” access for sensitive permissions and roles (that is, static access granted on day one of employment) and instead focus on moving that access to just-in-time (JIT). Just-in-time access allows end users to temporarily escalate permissions, privileges, or account creation, set for a pre-defined duration or justification. Your security is improved because users only have access when they truly need it. Compromised accounts have a reduced blast radius of attack. Your attack surface area has been reduced.
JIT provisioning is particularly relevant in the cloud era, where workloads and resources are constantly changing and access is controlled by the authorization controls of the services that the user is logging into. By automating the provisioning and deprovisioning of access based on contextual factors like user role and activity, security teams can reduce risk without impeding productivity. These perks are being confirmed across the industry. Ramp recently spoke about its switch to JIT, saying it “significantly impacted and benefited [their] organization," thanks to reduced vulnerability and increased user trust.
And there’s a bonus … reduce compliance pain
Compliance requirements can be onerous. By moving to just-in-time access for cloud infrastructure, apps, and roles, companies can also streamline and reduce the overhead of maintaining and meeting compliance requirements. Specifically, user access reviews are a process where users must review sensitive permissions and access levels on a regular basis. They’re an extremely useful tool for finding orphaned accounts and over permissioned users. However, they can also be a lot of work. JIT access allows you to make all sensitive roles and permissions ephemeral. This means users must always re-request and/or have a justification for access.
What’s next for privileged access management?
The era of traditional PAM approaches is coming to an end as static, shared accounts are being replaced by dynamic permission management and escalation. Combined with self-service, streamlined human in the loop and policy driven access controls, and automation for escalation and de-escalation, companies are not only achieving better security but better user experience as well.