
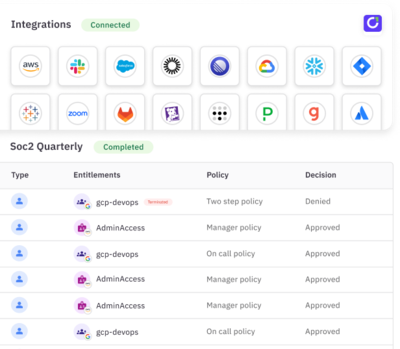
Four Ways to Use ConductorOne Automations to Strengthen Security
·Claire McKennaAutomate identity security with speed and precision. Learn how ConductorOne Automations help security teams reduce risk, enforce least privilege, and respond to high-risk access changes in real time without adding operational overhead.




Stay in touch
The best way to keep up with identity security tips, guides, and industry best practices.