Skip ahead to Baton on GitHub.
When we set out to build ConductorOne, we started with the idea that identity needs to shift left (check out the early blog post, Why Identity Needs to Shift Left). The shift left means focusing time and resources on preventing issues, before you have to detect and remediate. But how do you prevent an issue you can’t see coming? Visibility!
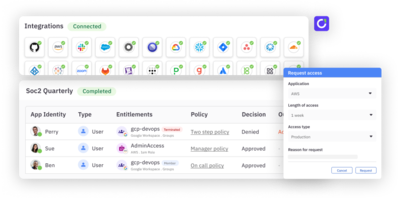
We’ve heard from our customers and have experienced first hand the pain of getting visibility into identity data – it’s tedious, time consuming, and sometimes nearly impossible to get a fine-grained view into details like user accounts, admins, permissions, roles, groups, repos, projects, resources, and more across apps. We too are tired of screenshots. We want less artisanal spreadsheets. The abundance of one-off Python scripting is not a positive thing! There are too many methods of extracting data and no single data model. And perhaps worst of all, this is a distributed people problem internally-–apps are owned by different humans, and not all of them want to take screenshots for you! We are tired of this, so today we’re passing the Baton, and announcing the first open source toolkit for auditing user access.
An introduction to Baton
Baton is an open source toolkit to extract, normalize, and interact with identity data from any app, with a standardized but extensible data model. Through the Baton CLI or SDKs, developers can audit infrastructure access on-demand, run diffs, and extract access data. This can be used for automating user access reviews, exports into SIEMs, real-time visibility, and more.
Today, we are releasing Baton connectors for Okta, AWS, GitHub, MySQL, and Postgres, with many more to come. We believe that both IaaS and SaaS need this—security visibility isn’t just an infrastructure problem. Baton also provides an SDK as a toolkit for developers to build new connectors for any application of their choice, including homegrown and back office applications. The connectors provide an automated way to extract data like user accounts, permissions, roles, groups, and other access details from applications in a single, standardized output file that can be extended to any identity security or governance project.
Baton use cases
Baton is extensible and helpful for a variety of use cases, but here are a few we’re excited about:
- Find all AWS IAM users with a specific IAM role
- Audit GitHub repo admins
- Find users in apps that aren’t in your IdP
- Detect differences or changes in permissions in GitHub or AWS
- Export GitHub permissions into a CSV for loading into a user access review
- Discover all access for a user or an account across all SaaS and IaaS apps
How to get started
Get started with a specific application by deploying the connector as a Docker image hosted on-prem or in the cloud and adding application credentials. Each connector provides the source code to audit behavior and data access for security purposes, and can also be forked to add custom sync, discovery, or provisioning logic. Use the SDK to start building a new connector, available in Go language, or any language using protocol buffers. To start using Baton, visit github.com/conductorone/baton or learn more in our documentation.
In relation to ConductorOne
We’re passionate about eliminating the tradeoff between security and productivity when it comes to identity. We want to solve the hard problems–what you do with your identity data, how you implement least privilege, how you move closer to zero trust–not just the act of getting identity data out of your applications. We believe that accessing identity data should be a fast, easy, repeatable process for everyone, which is why we’re open sourcing the work we’ve put in over the last two years building connectors for our own platform.
ConductorOne is the orchestration and automation plane for your access controls, while Baton provides the bridge between a control plane (whether you decide to use ConductorOne or not) and the identity data in your infrastructure and applications.
Join us
We welcome contributions, and ideas, no matter how small – our goal is to make identity and permissions sprawl less painful for everyone. Baton is licensed under the Apache 2.0, an OSI-approved Open Source License, because we want to enable widespread contributions and a broad community who cares about security outcomes to participate. See CONTRIBUTING.md on GitHub for more details.