Unleash the power of autonomous identity governance
App sprawl, non-human identities, and AI are exploding your identity count. ConductorOne secures them all.
Trusted by IT and Security @







Identities are growing exponentially
Your identity landscape
is growing faster than
your legacy tools can handle.
ConductorOne makes
identity management effortless.
effortless.
 effortless.
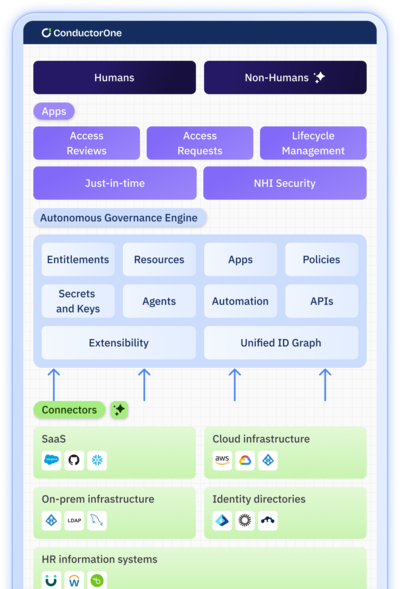
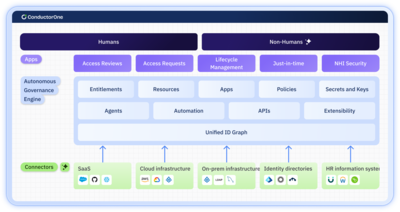
effortless.What is the ConductorOne Autonomous Governance Engine (AGE)?
Agentic Powered
Manage identities at massive scale with the first multi-agent identity platform.
Open Connectivity
The most out-of-the-box connectors. Connectivity to the platform is open to any app or technology.
Extensible
Customize ConductorOne to fit your organizational needs.
Unified Identity Control
Ingest all entitlement, resource, and identity data into a single unified data model.
applications
One platform to power your identity use cases
Lifecycle management
Simplify security and compliance with a governance solution built for today’s environments. Centralize and manage all your identities with flexible policies, dynamic access controls, risk notifications, and smart access reviews.
Learn more
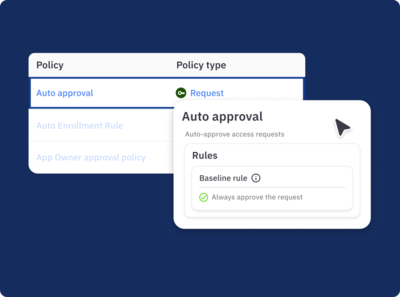
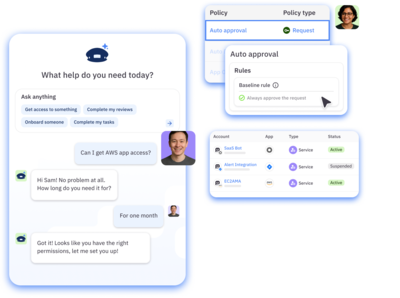
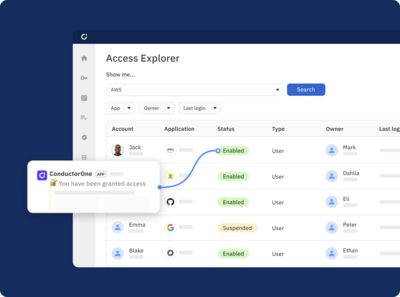
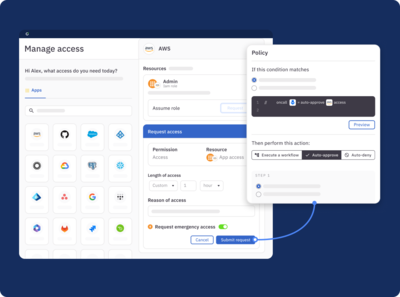
Access requests
Live the dream—secure access control, no friction. Automate fine-grained provisioning and create custom policies that streamline approvals and revocations. Make it easy for users to self-service, and dynamically adjust access as roles and attributes change.
Learn more
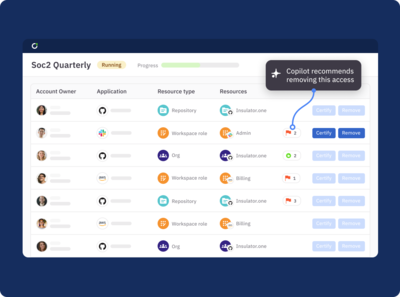
Access reviews
Save hours of work and streamline audits. Precisely scope and run fully automated reviews, provide risk insights for reviewers, verify data accuracy, and generate auditor-ready reports in a click.
Learn more
Just-in-time access
Secure sensitive access without slowing users down. Automate self-service JIT access to any resource and create context-driven policies for on-call and break-glass access that make it easy for users to get critical access when needed.
Learn more
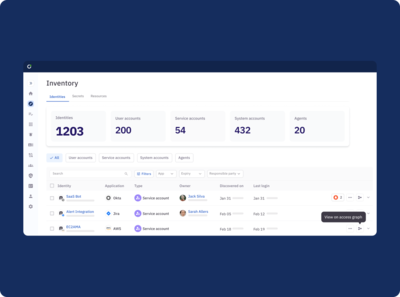
NHI
No more blind spots. Inventory, manage, and remediate risks for AI agents and NHIs like service accounts, keys, tokens, certificates, and more.
Learn more
Connect your entire ecosystem
- Directories
- On-prem
- Cloud
- Infrastructure
- Helpdesk
Integrate all your cloud and on-prem apps and infrastructure, including legacy and private applications. Connect most apps in minutes and get fully set up in weeks—not months.