Scale access at the speed of AI
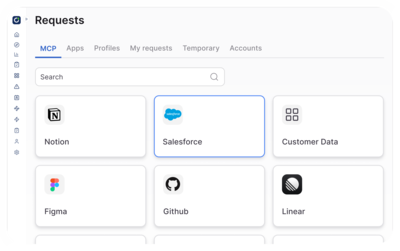
Control human and agent access across apps, infrastructure, and MCPs
Trusted by It and Security @














Welcome to the agentic era
Traditional identity tools were built for human speed.
The AI era demands:
Agentic identity management
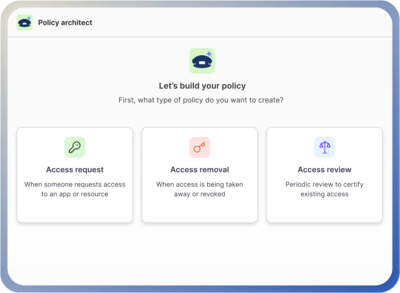
Policy-driven access controls
Intent-based approvals
ConductorOne is the identity platform for humans and agents, built for AI scale.

See everything
Know and govern every action happening in your environment.
Universal identity graph across users, services, agents, API keys
Real-time activity monitoring for humans and agents
Audit-ready logging

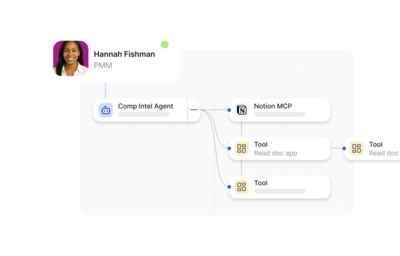
Decide in real time
Secure access with real-time policy enforcement and fine-grained authorization.
Policy-as-code that enforces guardrails across every system
App, data, entitlement, and fine-grained tools authorization
MCP self-service with policy-driven tool enforcement
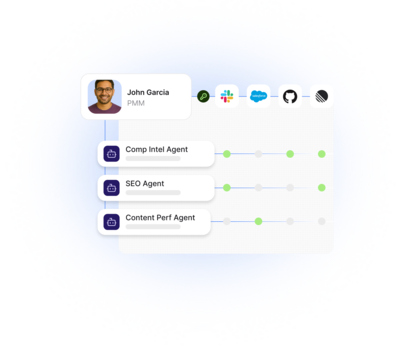
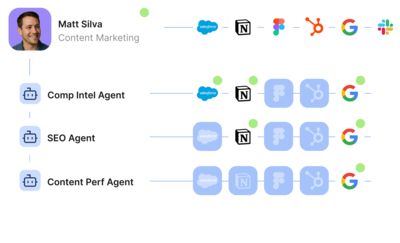
Govern every identity
Manage every human, AI agent, and service account in one platform.
AI agent fleet management with central governance controls
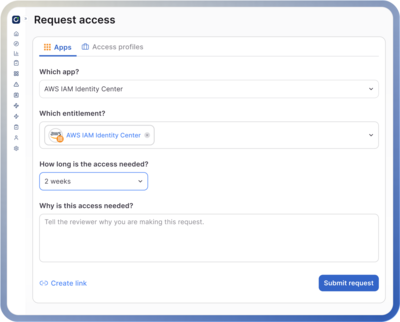
Dynamic access provisioning based on trust and context
Lifecycle automations for agents, service accounts, and human users
Go faster without adding headcount
Automate approvals, workflows, and access management without more tickets and people.
Automated approvals with human oversight for sensitive actions
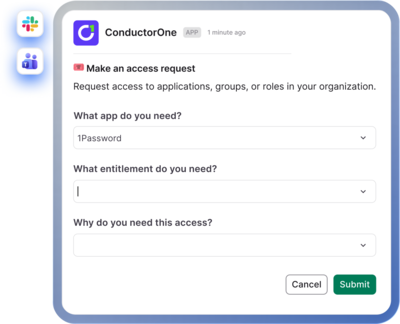
Apps, AI tools, and MCP self-service
Build and deploy agents faster and more securely
Use Case Explorer

Manage access for agents and AI tools to business data, cloud app, and infrastructure
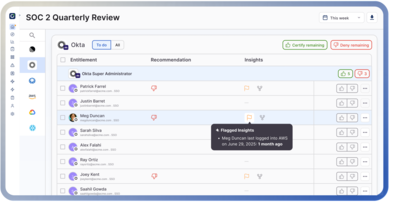
AI driven governance workflows and policy controls
Provision accounts, entitlements, and permissions for only as long as they are needed
Eliminate rubber stamping and unnecessary clicks with risk-based, AI-driven access reviews
Eliminate helpdesk tickets through AI agent and self-service workflows
Every system. Every identity.
One control plane.
Apps, infrastructure, MCPs, data sources—connected in minutes, not months.
The best thing about C1?